The Sentinel Paradigm: Evolutionary Cryptography, Quantum Disruptions, and the Re-Architecting of Global Signal Intelligence
The global architecture of information security is currently undergoing a foundational shift, transitioning from a period of relative classical stability to an era of quantum uncertainty. This transformation is not merely a technical upgrade but a profound realignment of the mechanisms by which state actors secure their secrets and exploit those of their adversaries. To understand the current state of encryption and decryption technology, one must trace the evolution of signal intelligence (SIGINT) from the analog microwave relays of the 1980s to the contemporary reality of the "Internet Backbone" exploitation. This historical context provides the necessary framework for analyzing the emergence of quantum computing—a development that threatens the mathematical assumptions underpinning modern civilization. As state actors increasingly engage in retrospective collection strategies, the urgency of transitioning to post-quantum standards has moved from a theoretical concern to a mandatory regulatory and geopolitical priority.
The Contemporary Cryptographic Estate: Standards of the 2025 Transition
As of 2025, the state of data encryption is characterized by a transition from traditional legacy protocols to high-assurance standards designed to resist both sophisticated classical attacks and emerging quantum threats. Regulatory frameworks, such as the Health Insurance Portability and Accountability Act (HIPAA) updates of 2025, have moved from recommending encryption to mandating it for all data at rest and in transit.1 The primary symmetric benchmark remains the Advanced Encryption Standard (AES) with a 256-bit key length. AES-256 is recognized for its high efficiency and virtually infinite resistance to classical brute-force attempts, requiring  operations to crack, a feat that remains computationally impossible for any existing or foreseeable classical supercomputer.2
operations to crack, a feat that remains computationally impossible for any existing or foreseeable classical supercomputer.2
For asymmetric encryption, which handles key exchanges and digital signatures, the industry is seeing a shift toward larger key sizes and more efficient mathematical foundations. RSA-2048, once the gold standard, is now viewed as the absolute minimum requirement, with a preference for RSA-4096 or Elliptic Curve Cryptography (ECC).1 ECC is particularly favored for resource-constrained environments like mobile devices and Internet of Things (IoT) sensors, as a 256-bit ECC key offers security equivalent to a 3072-bit RSA key, significantly reducing the computational overhead for authentication.3
Encryption Layer | Primary Algorithm | Regulatory Status (2025) | Security Strength | Performance Impact |
Data at Rest | AES-256 | Required (HIPAA/GDPR) | Extremely High | Minimal (Hardware accelerated) |
Data in Transit | TLS 1.3 | Mandatory for new systems | High (Forward Secrecy) | Minimal |
Key Exchange | RSA-4096 | Recommended | High | Moderate to High |
Mobile/IoT | ECC P-384 | Recommended | High | Very Low |
Legacy Systems | AES-128 | Acceptable for non-critical | Moderate | Extremely Low |
The 2025 mandates reflect a broader understanding that encryption must be pervasive. This includes the implementation of Transparent Data Encryption (TDE) for databases and file-level encryption using AES-256-GCM to ensure both confidentiality and data integrity.1 These standards form the "classical" baseline that is currently being challenged by the advent of quantum-capable adversaries.
The Evolution of Signal Intelligence: 1980s Analog to Modern Digital Exploitation
The methodology of military and state-sponsored signal intelligence has undergone a radical transformation since the 1980s. During the late Cold War period, SIGINT was largely focused on the interception of radio frequency (RF) communications and microwave relays.5 The technological landscape was defined by a widening gap between the United States and its adversaries, particularly the Soviet Union. By 1983, Soviet leadership, including Chief of General Staff Marshal Nikolai Ogarkov, recognized that the Soviet Union had lost the computer arms race. Ogarkov observed that American children were playing with computers before they began school, while the Soviet Defense Ministry lacked computers in every office.6 This technological disparity forced adversaries to rely on stolen or bought technology rather than indigenous innovation, a dynamic that continues to shape modern cyber-espionage.6
The Shift from Microwave to Fiber and Packet Switching
The transition from analog to digital warfare began with the development of the Internet, which evolved from the military's ARPANET in 1969. The introduction of packet switching technology was a critical milestone, allowing electronic communications to be divided into packets and routed through a distributed network without a single point of failure.7 As telecommunications moved from copper wires and microwave towers to fiber-optic cables in the 1980s, the physical nature of interception changed. The first transatlantic fiber-optic cable, TAT-8, became operational in 1988, signaling the end of the satellite-dominant era for international telephony and data.8
Modern SIGINT exploitation now focuses on the "Internet Backbone"—the massive undersea cables and land-based switching stations that carry over 99% of all international data traffic.10 Unlike the localized radio intercepts of the 1980s, modern SIGINT relies on "Upstream" collection, where agencies tap directly into the fiber-optic infrastructure as data flows past.11
SIGINT Era | Primary Target | Interception Method | Key Technology |
1980s (Analog) | Radio, Microwave Relays | RF Intercept, Microwave Tapping | Specialized Receivers, Tape Storage |
1990s (Hybrid) | Early Internet, Fiber | SBU Tapping, Server Exploits | Packet Analyzers, T1/T3 Links |
2000s (Digital) | Internet Backbone | Upstream Collection, PRISM | Fiber Taps, Semantic Analyzers |
2020s (Quantum) | Encrypted Archives | Bulk Harvesting, HNDL | High-Volume Storage, Q-Ready Nodes |
Programs like FAIRVIEW and BLARNEY represent the operational reality of this evolution, where state agencies collaborate with telecommunications providers to install "sniffer" software and semantic traffic analyzers at major switching facilities.11 These devices, such as the Narus Semantic Traffic Analyzer (STA 6400), filter petabytes of traffic using "strong selectors"—IP addresses, email headers, and phone numbers—to identify and archive communications of interest.13
The Quantum Paradigm Shift: Redefining Bit-Security
Quantum computing introduces a fundamental shift in computational power that renders current asymmetric encryption vulnerable. While classical computers process information as binary bits (0 or 1), quantum computers use qubits, which can exist in a state of superposition—being both 0 and 1 simultaneously.14 Through the principle of entanglement, qubits can be linked such that the state of one instantly influences another, regardless of distance. This allows quantum systems to perform massive parallel computations that are ideally suited for breaking the mathematical problems upon which modern cryptography rests.14
Shor’s Algorithm and the End of RSA
The most significant threat to modern encryption is Shor’s algorithm, proposed by Peter Shor in 1994. Shor’s algorithm can efficiently factor large integers and solve discrete logarithm problems in polynomial time—tasks that would take classical supercomputers trillions of years.15 In a mature quantum era, a cryptographically relevant quantum computer (CRQC) running Shor's algorithm could break a 2048-bit RSA key in a matter of seconds or minutes.17
Recent breakthroughs have significantly accelerated the timeline for this threat. In June 2025, researcher Craig Gidney published a paper demonstrating that software optimizations could allow a quantum computer with fewer than one million qubits to break RSA-2048—a dramatic reduction from previous estimates of 20 million qubits.19 This development effectively moved the "Q-Day" estimate (the day current encryption fails) closer, with some projections now suggesting the mid-2030s.19
Grover’s Algorithm and Symmetric Erosion
While Shor’s algorithm targets asymmetric encryption, Grover’s algorithm provides a quadratic speedup for brute-force attacks on symmetric ciphers like AES.16 Grover’s algorithm reduces the effective security level of a symmetric key by half; for example, AES-128 is reduced to the security equivalent of a 64-bit key, which is considered highly vulnerable.17 To maintain the same level of security in a post-quantum world, organizations must double their key lengths, making AES-256 the minimum standard for long-term data protection.17
Retrospective Espionage: "Harvest Now, Decrypt Later" (HNDL)
A critical component of modern state-actor behavior is the "Harvest Now, Decrypt Later" (HNDL) strategy. This involves the mass collection and storage of currently unreadable encrypted data with the intent of decrypting it once quantum computers reach maturity.18 This strategy reframes the quantum threat from a future concern to a present-day risk, particularly for data with long confidentiality lifetimes.21
The Lifecycle of HNDL
The HNDL process consists of three distinct phases that state actors are currently executing with varying levels of intensity.
- Harvesting: This phase involves the quiet acquisition of encrypted information through network traffic interception, server breaches, and tapping into the global Internet backbone.22 Attackers target government secrets, intellectual property, financial records, and healthcare data.18
- Storage: The harvested data is moved to massive, often state-run repositories where it is archived for years or decades.22 The simplicity of this phase—where "time does the rest"—makes it nearly impossible to detect once the data has left the original network.22
- Decryption: Once a CRQC becomes available, the centralized data will be processed using Shor's and Grover's algorithms to unlock historical communications, revealing passwords, strategic plans, and personal identifiers.23
Vulnerable Repositories and State Objectives
State actors, such as those in China and Russia, are particularly focused on HNDL because the strategic value of government and diplomatic secrets does not diminish over a 10-to-20-year window.18 Furthermore, distributed ledgers and cryptocurrency networks are highly vulnerable to harvesting. Because these ledgers are public and permanent, a bad actor can archive a replica of the entire blockchain today and wait for quantum technology to reveal the identities and private transactions of users in the future.14
Securing the Future: Post-Quantum Cryptography (PQC)
To counter the quantum threat, the National Institute of Standards and Technology (NIST) has led a global effort to standardize Post-Quantum Cryptography (PQC)—mathematical algorithms designed to be secure against both classical and quantum computers.25 These algorithms are generally based on different mathematical assumptions than RSA or ECC, specifically focusing on lattice-based, hash-based, and code-based problems.27
The First Wave of PQC Standards (2024–2025)
In August 2024, NIST finalized the first set of PQC standards (FIPS 203, 204, and 205), marking the beginning of the global migration.25 These standards represent the "first wave" of quantum-resistant security.
FIPS Standard | Algorithm Family | Original Name | Primary Purpose |
FIPS 203 | Module-Lattice | ML-KEM (Kyber) | Key establishment/Encryption |
FIPS 204 | Module-Lattice | ML-DSA (Dilithium) | Digital Signatures |
FIPS 205 | Stateless Hash | SLH-DSA (SPHINCS+) | High-security Signatures |
FIPS 206 | FFT NTRU | FN-DSA (FALCON) | Compact Signatures |
Lattice-based cryptography is the foundation of the primary standards, leveraging the hardness of problems like "Learning With Errors" (LWE). LWE involves solving linear equations where small, random errors have been added, a task that remains difficult for quantum computers.28 These algorithms provide a balance of security and performance, though they require significantly larger keys and more computational power than classical methods.30
Alternative Paradigms: Code-Based and Hash-Based
Beyond lattices, NIST is standardizing alternative "backups" to ensure diversity in the cryptographic estate. Code-based systems, such as the Classic McEliece and HQC (selected in March 2025), rely on the difficulty of decoding random linear codes—a problem that has withstood over 40 years of cryptanalysis.25 While McEliece public keys are massive (up to 1 megabyte), they offer exceptionally fast decryption and a high security margin.27 Hash-based signatures, such as SLH-DSA, derive their strength from the proven hardness of reversing modern hash functions, making them a conservative and "battle-tested" choice for long-term assurance.27
Physical Layer Security: Quantum Key Distribution (QKD)
While PQC relies on mathematical complexity, Quantum Key Distribution (QKD) relies on the laws of physics. QKD uses the "no-cloning theorem" of quantum mechanics—the principle that an unknown quantum state cannot be perfectly copied without being disturbed.34 By sending information via photons, any attempt by an eavesdropper to intercept the key will be immediately detected by the legitimate parties, who can then discard the compromised session.34
Global Adoption and Strategic Divergence
The adoption of QKD has created a geopolitical divide. The United States and its "Five Eyes" allies (UK, Canada, Australia, NZ) have largely prioritized PQC, with the NSA and NCSC explicitly advising against QKD for national security systems.37 Their concerns center on QKD's requirement for specialized hardware, its limited range (requiring "trusted nodes" that introduce new vulnerabilities), and its inability to perform identity authentication without classical cryptographic help.35
In contrast, China and the European Union are investing heavily in QKD as a "defense in depth" strategy. China’s Micius satellite, launched in 2016, demonstrated the first space-to-ground QKD link over 1,200 miles.39 Europe is developing its own satellite constellation, Eagle-1, as part of the EuroQCI initiative to safeguard critical infrastructure by 2030.39
Feature | Post-Quantum Cryptography (PQC) | Quantum Key Distribution (QKD) |
Security Basis | Mathematical Hardness | Principles of Physics |
Infrastructure | Standard Classical Networks | Dedicated Fiber/Satellites |
Deployment | Software Update/Firmware | New Hardware/Lasers |
Authentication | Built-in | Requires external classic protocol |
Range | Global | Limited (Point-to-point) |
The Mature Quantum Era: Integrated Security Frameworks
When quantum computing matures, data security will not rely on a single algorithm but on a layered, "crypto-agile" architecture. Crypto-agility is defined as the ability of a system to quickly replace or adapt cryptographic algorithms without interrupting the flow of a running system.42 This agility is essential because new research can catastrophically break even promising PQC candidates, as seen with the SIKE algorithm in 2022.30
Migration Timelines and Costs
The transition to quantum-safe standards is a labor-intensive and expensive process. The US government has established a timeline to deprecate 112-bit security algorithms after 2030 and mandate a full transition to quantum-resistant systems by 2035.20 For large organizations, this involves a multi-phase roadmap:
- Inventory: Identifying every device, certificate, and hardcoded cryptographic call across the enterprise, including legacy IoT and industrial control systems.27
- Hybrid Deployment: Implementing protocols like TLS 1.2 or 1.3 with a combination of classical and PQC methods (e.g., RSA + Kyber) to ensure backward compatibility and security during the transition.5
- Supply Chain Management: Ensuring that third-party vendors, cloud providers, and certificate authorities are also quantum-ready, as an organization's security is only as strong as its weakest vendor.30
The financial implications are staggering, with some estimates suggesting that upgrading the cryptographic estate for a large telecommunications firm could take over 10 years and cost hundreds of millions of dollars.30 Organizations that delay this transition risk "cryptographic debt," where the cost and complexity of the upgrade increase exponentially as legacy systems become more entrenched.30
Technical Nuances of Next-Generation Algorithms
To appreciate the complexity of the 2025 standards, one must examine the specific mechanics of the "Learning With Errors" (LWE) and code-based paradigms.
LWE and Module-LWE (ML-KEM)
In a standard LWE system, a matrix  and a vector
and a vector  are used to generate a public key
are used to generate a public key 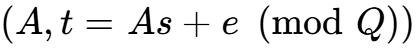 , where
, where  is a small error vector.31 The presence of this "noise" makes it computationally hard to recover
is a small error vector.31 The presence of this "noise" makes it computationally hard to recover  from
from  .29 ML-KEM (CRYSTALS-Kyber) uses a "Module" variant of LWE, which introduces additional algebraic structure to make the matrices more compact and the operations faster, albeit at the risk that this structure might one day be exploited by a specialized quantum attack.29 Consequently, some high-security advocates prefer "unstructured" lattice schemes like FrodoKEM, which are slower but offer a more conservative security profile.29
.29 ML-KEM (CRYSTALS-Kyber) uses a "Module" variant of LWE, which introduces additional algebraic structure to make the matrices more compact and the operations faster, albeit at the risk that this structure might one day be exploited by a specialized quantum attack.29 Consequently, some high-security advocates prefer "unstructured" lattice schemes like FrodoKEM, which are slower but offer a more conservative security profile.29
Code-Based Mechanisms (HQC and BIKE)
Code-based KEMs like HQC (Hamming Quasi-Cyclic) utilize error-correcting codes. In HQC, a random array  and vectors
and vectors  are chosen.44 The public key is
are chosen.44 The public key is 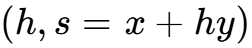 , while the private key is
, while the private key is  .44 During encapsulation, a message
.44 During encapsulation, a message  is encoded using a generator matrix
is encoded using a generator matrix  and combined with
and combined with  and a noise vector
and a noise vector  .44 Decryption uses the private key to remove the "noise" and recover the original message. This family is favored for its mature security analysis and resistance to lattice-specific attacks.27
.44 Decryption uses the private key to remove the "noise" and recover the original message. This family is favored for its mature security analysis and resistance to lattice-specific attacks.27
Conclusion: The Horizon of Digital Trust
The evolution of data encryption and signal intelligence has brought the global community to a critical inflection point. The transition from the localized microwave intercepts of the 1980s to the bulk "Upstream" collection of the digital age has empowered state actors with unprecedented reach. This power is now being funneled into the "Harvest Now, Decrypt Later" strategy, creating a ticking clock for organizations with sensitive, long-life data.
The paradigm shift introduced by quantum computing is not merely a quantitative increase in speed but a qualitative change in how mathematical problems are solved. Shor’s algorithm represents a definitive end-date for the current asymmetric status quo. In response, the standardization of Post-Quantum Cryptography through the NIST process provides a necessary, if complex, path forward. Securing data in a mature quantum era will require a multi-layered approach: reinforcing the physical layer with QKD where appropriate, adopting high-assurance PQC standards like ML-KEM and ML-DSA, and maintaining a state of perpetual crypto-agility. As state actors and criminal organizations continue to build their encrypted archives, the speed at which the global community migrates to these new standards will determine the long-term viability of digital privacy and national security in the 21st century.
Works cited
- HIPAA Encryption Protocols: 2025 Updates | Censinet, Inc., accessed February 4, 2026, https://censinet.com/perspectives/hipaa-encryption-protocols-2025-updates
- Why AES-256 Encryption Still Matters (Especially for Regulated Industries) - TerraZone, accessed February 4, 2026, https://terrazone.io/aes-256-encryption/
- Encryption Best Practices 2025: Guide to Data Protection - Training Camp, accessed February 4, 2026, https://trainingcamp.com/articles/encryption-best-practices-2025-complete-guide-to-data-protection-standards-and-implementation/
- Encryption in 2025: Trends & Best Practices - Ciphertex Data Security, accessed February 4, 2026, https://ciphertex.com/2025/07/21/encryption-in-2025-trends-best-practices/
- Signals intelligence in modern history - Wikipedia, accessed February 4, 2026, https://en.wikipedia.org/wiki/Signals_intelligence_in_modern_history
- Cold War Computer Arms Race - Marine Corps University, accessed February 4, 2026, https://www.usmcu.edu/Outreach/Marine-Corps-University-Press/MCU-Journal/JAMS-vol-14-no-2/Cold-War-Computer-Arms-Race/
- Technology and Law: The Evolution of Digital Warfare, accessed February 4, 2026, https://digital-commons.usnwc.edu/cgi/viewcontent.cgi?article=1402&context=ils
- Submarine communications cable - Wikipedia, accessed February 4, 2026, https://en.wikipedia.org/wiki/Submarine_communications_cable
- Undersea Telecommunication Cables: Technology Overview and Issues for Congress, accessed February 4, 2026, https://www.congress.gov/crs-product/R47237
- Submarine Cables, Cybersecurity and International Law: An Intersectional Analysis, accessed February 4, 2026, https://scholarship.law.edu/cgi/viewcontent.cgi?params=/context/jlt/article/1001/&path_info=Davenport.pdf
- Strict rules help U.S. access data traffic on undersea cables - The Japan Times, accessed February 4, 2026, https://www.japantimes.co.jp/news/2013/07/07/business/tech/strict-rules-help-u-s-access-data-traffic-on-undersea-cables/
- Submarine cables and the oceans: connecting the world, accessed February 4, 2026, https://www.iscpc.org/documents/?id=132
- Upstream collection - Wikipedia, accessed February 4, 2026, https://en.wikipedia.org/wiki/Upstream_collection
- "Harvest Now Decrypt Later": Examining Post-Quantum Cryptography and the Data Privacy Risks for Distributed Ledger Networks - Federal Reserve Board, accessed February 4, 2026, https://www.federalreserve.gov/econres/feds/files/2025093pap.pdf
- Quantum Computing and Cryptography: An Analysis of Shor's Algorithm - ByteBridge, accessed February 4, 2026, https://bytebridge.medium.com/quantum-computing-and-cryptography-an-analysis-of-shors-algorithm-66980e3c8d10
- accessed February 4, 2026, https://blogs.cisco.com/developer/how-post-quantum-cryptography-affects-security-and-encryption-algorithms#:~:text=The%20primary%20threats%20to%20current,force%20attacks%20against%20symmetric%20encryption.
- A Comparative Study of Classical and Post-Quantum Cryptographic Algorithms in the Era of Quantum Computing - arXiv, accessed February 4, 2026, https://arxiv.org/html/2508.00832v1
- What You Need to Know About "Harvest-Now, Decrypt-Later" Attacks - AppViewX, accessed February 4, 2026, https://www.appviewx.com/blogs/what-you-need-to-know-about-harvest-now-decrypt-later-attacks/
- State of the post-quantum Internet in 2025 - The Cloudflare Blog, accessed February 4, 2026, https://blog.cloudflare.com/pq-2025/
- How Post-Quantum Cryptography Affects Security and Encryption Algorithms - Cisco Blogs, accessed February 4, 2026, https://blogs.cisco.com/developer/how-post-quantum-cryptography-affects-security-and-encryption-algorithms
- Harvest now, decrypt later - Wikipedia, accessed February 4, 2026, https://en.wikipedia.org/wiki/Harvest_now,_decrypt_later
- Harvest Now, Decrypt Later (HNDL): The Quantum-Era Threat - Palo Alto Networks, accessed February 4, 2026, https://www.paloaltonetworks.com/cyberpedia/harvest-now-decrypt-later-hndl
- Harvest now, decrypt later attacks & the quantum threat | Sectigo® Official, accessed February 4, 2026, https://www.sectigo.com/blog/harvest-now-decrypt-later-quantum-threat
- Report: China May Steal Encrypted Government Data Now to Decrypt with Quantum Computers Later - Nextgov/FCW, accessed February 4, 2026, https://www.nextgov.com/emerging-tech/2021/11/report-china-may-steal-encrypted-government-data-now-decrypt-quantum-computers-later/187020/
- Post-Quantum Cryptography | CSRC, accessed February 4, 2026, https://csrc.nist.gov/projects/post-quantum-cryptography/post-quantum-cryptography-standardization
- Post-Quantum Cryptography | CSRC - NIST Computer Security Resource Center, accessed February 4, 2026, https://csrc.nist.gov/projects/post-quantum-cryptography
- What Is Post-Quantum Cryptography (PQC)? A Complete Guide - Palo Alto Networks, accessed February 4, 2026, https://www.paloaltonetworks.com/cyberpedia/what-is-post-quantum-cryptography-pqc
- What is lattice-based cryptography? | Sectigo® Official, accessed February 4, 2026, https://www.sectigo.com/blog/what-is-lattice-based-cryptography
- FrodoKEM: A conservative quantum-safe cryptographic algorithm - Microsoft Research, accessed February 4, 2026, https://www.microsoft.com/en-us/research/blog/frodokem-a-conservative-quantum-safe-cryptographic-algorithm/
- Challenges of Upgrading to Post-Quantum Cryptography (PQC), accessed February 4, 2026, https://postquantum.com/post-quantum/pqc-challenges/
- Prepping for post-quantum: a beginner's guide to lattice cryptography - The Cloudflare Blog, accessed February 4, 2026, https://blog.cloudflare.com/lattice-crypto-primer/
- NIST PQC: The Road Ahead, accessed February 4, 2026, https://csrc.nist.gov/csrc/media/Presentations/2025/nist-pqc-the-road-ahead/images-media/rwcpqc-march2025-moody.pdf
- Post-quantum cryptography - Wikipedia, accessed February 4, 2026, https://en.wikipedia.org/wiki/Post-quantum_cryptography
- What Is Quantum Key Distribution (QKD)? + How It Works - Palo Alto Networks, accessed February 4, 2026, https://www.paloaltonetworks.com/cyberpedia/quantum-key-distribution-qkd
- Google's Commitment to a Quantum-Safe Future: Why PQC is Google's Path forward and not QKD, accessed February 4, 2026, https://bughunters.google.com/blog/googles-commitment-to-a-quantum-safe-future-why-pqc-is-googles-path-forward-and-not-qkd
- The importance of quantum-safe communication: post quantum cryptography (PQC) and quantum key distribution (QKD), accessed February 4, 2026, https://www.toshiba.eu/quantum/insights/the-importance-of-qkd-and-pqc-for-quantum-security/
- Quantum Key Distribution (QKD): Why Countries Differ on Its Future, accessed February 4, 2026, https://postquantum.com/post-quantum/qkd-countries-differ/
- Are Enterprises Ready for Quantum-Safe Cybersecurity? - arXiv, accessed February 4, 2026, https://arxiv.org/html/2509.01731v1
- The global quantum space race - SPIE, accessed February 4, 2026, https://spie.org/news/photonics-focus/janfeb-2025/racing-for-quantum-supremacy-in-space
- The state of U.S.-China quantum data security competition - Brookings Institution, accessed February 4, 2026, https://www.brookings.edu/articles/the-state-of-u-s-china-quantum-data-security-competition/
- ESA and European Commission to build quantum-secure space communications network, accessed February 4, 2026, https://www.esa.int/Applications/Connectivity_and_Secure_Communications/ESA_and_European_Commission_to_build_quantum-secure_space_communications_network
- Quantum disentangled #1: “Harvest now, decrypt later” - The quantum threat is already here, accessed February 4, 2026, https://technologyquotient.freshfields.com/post/102lx4l/quantum-disentangled-1-harvest-now-decrypt-later-the-quantum-threat-is-alr
- 2024-2025 CRA Quad Paper: The Post-Quantum Cryptography Transition: Making Progress, But Still a Long Road Ahead - Computing Research Association, accessed February 4, 2026, https://www.cra.org/wp-content/uploads/2025/01/2024-2025-CRA-Quad-Paper_-The-Post-Quantum-Cryptography-Transition_-Making-Progress-But-Still-a-Long-Road-Ahead.pdf
- Post-quantum cryptography: Code-based cryptography - Red Hat, accessed February 4, 2026, https://www.redhat.com/en/blog/post-quantum-cryptography-code-based-cryptography
